TL; DR: The Quick Version
- PKI is a system that gives IoT devices a digital identity.
- Device certificate authentication is the process of verifying that identity.
- IoT mutual TLS ensures that both the device and the server trust each other before sharing any data.
- Bottom line: Without PKI, your IoT network is just a collection of vulnerable “open doors.”
Direct Answer of how PKI works in IoT devices?
What is PKI in IoT and how does it work? Here is the direct answer without fluff;
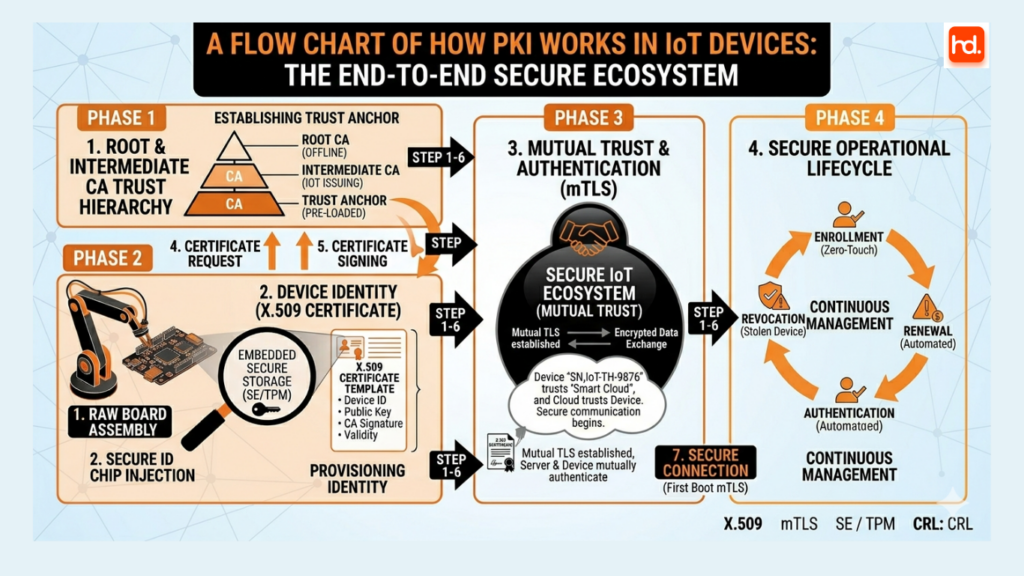
PKI (Public Key Infrastructure) in IoT enables an automated security system in which every device is assigned a unique, verifiable identity. This eliminates the use of passwords and provides secure access to the “Machine-to-Machine” communication layer.
Summary of Key Points Identity: Each device is given a unique Private Key, stored securely inside the device, and a Digital Certificate, which is the public identity.
Authentication: When a device wants to connect to a network, it proves to the network that it is a legitimate and authorized device, not a “spoofed” device trying to impersonate a legitimate device.
Encryptioauthorisedn: PKI enables Mutual TLS (mTLS) to ensure that all data traveling from the device to the cloud is encrypted and cannot be accessed by unauthorized parties.
Lifecycle Management: This enables the automated process of “enrolling” new devices and “revoking” compromised ones, making it scalable to millions of devices.
Detailed information about how PKI works in IoT Devices?
In the rapidly expanding world of the Internet of Things, every connected device, from a smart thermostat to an industrial robotic arm, needs a way to prove it belongs to your network. Without a solid “ID system,” your network is essentially an open door for hackers.
This is where PKI works in IoT devices becomes the foundation of modern digital safety. PKI (Public Key Infrastructure) isn’t just a technical hurdle; it’s the framework that allows thousands of devices to communicate securely without human intervention.
The Core Concept: The Digital Passport
Imagine an IoT device arriving at your facility. How does your server know it’s a legitimate piece of hardware and not a malicious “imposter” device?
PKI provides every device with a Digital Certificate. Think of this as a passport. It contains:
- The device’s unique ID.
- The manufacturer’s “official stamp” (Digital Signature).
- A public key used for secure communication.
How PKI Works in IoT Devices: The Three Pillars of Trust
To understand PKI IoT security, you must look at how these three elements interact:
1. Device Identity
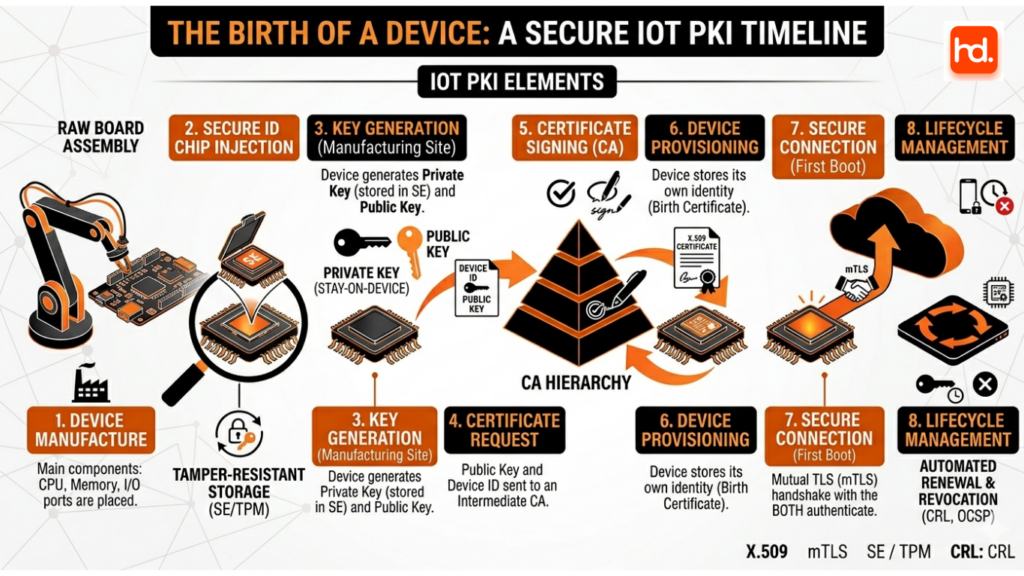
Every device is born with a unique identity. During manufacturing, a “Private Key” is securely generated and stored inside the device (often in a tiny, tamper-proof chip). This key never leaves the device. The corresponding “Public Key” is put into a certificate.
2. Device Certificate Authentication
When the device tries to connect to your cloud or home network, it presents its certificate. The network doesn’t just take the device’s word for it; it uses device certificate authentication to verify the digital signature against a trusted Authority. If the “stamp” is real, the device is let in.
3. IoT Mutual TLS (The “Secret Handshake”)
Standard website security (HTTPS) usually only proves that the server is real. However, in the IoT world, we use IoT mutual TLS (mTLS).
- The Server proves its identity to the Device.
- The Device proves its identity to the Server.
- It’s a two-way street of trust that ensures no eavesdroppers can jump into the middle of the conversation.
How PKI Works in IoT Devices and Why This Matters for Your Business
If you are managing a fleet of devices, how PKI works in IoT devices determines how much time you spend fighting fires versus growing your brand.
Security at Scale: You can’t manually set passwords for 10,000 sensors. PKI automates trust.
Preventing Rogue Devices: If a sensor is stolen or tampered with, you can “revoke” its certificate, instantly cutting its access to your data.
Data Integrity: Because of the encryption involved, you can be 100% sure the data coming from your “Logistics Tracker” hasn’t been changed by a third party.
Ready to Secure Your IoT Ecosystem?
To design a secure and scalable network, it is essential to possess both technical expertise and a “security-first” approach. At HireDeveloper.dev, we can assist you in creating the infrastructure you need to grow your business without compromises.
If you need experts to implement PKI IoT security, we’re here to help you get it right from day one.




